
Block1: Admit you have a Problem.
If someone asked you, “How do you know your server’s aren’t being exploited, right now?”. How would you respond? The truth is, most businesses don’t even find out until after the major credit card processors have called. Hundreds of credit cards making fraud purchases that were all tracked back to one business. I don’t know about you, but I wouldn’t like that feeling, knowing I was contributing to an underground criminal ring. These credit card processors can virtually shut you down, stopping all payments until you can prove to them the situation has been dealt with.
For now, lets assume it was your business under review. If you’re not with Hostek, you probably don’t even have a security specialist available, and if you do, I can only imagine the cleanup cost. One thing is for sure, if you don’t have an experienced security specialist, you will never be 100% sure that the cleanup was successful, or even permanent. The worst kind of hackers and exploits don’t even want you to know they are present, stealing credit card numbers, personal data, and injecting code that will infect other machines. This is big business and they have ways of doing it without detection.
Block2: Take the Next Step
Now that you know what’s at stake, I hope you’ve decided to be proactive. I hope your willing to take the next step. If you keep reading this article there are several building blocks that will help ensure your Cloud environment is as secure as possible. With a little work, you may just avoid these types of breaches. If it becomes too technical for you, open a ticket or give us a call, and we will help ensure you make it through the process.
Block3: Separate Management Access
In the Cloud, users communicate with applications through open ports on servers. There are roughly 65,000 ports that could be listening on any given server. Some ports are considered more vulnerable than others. Its not the ports that are vulnerable though, it’s the applications that are listening on them. Some of these applications are meant for LAN communication, while others are meant for WAN communication. It’s important that you don’t have LAN applications listening on the WAN, because they are most susceptible. But even some WAN applications can be unsafe in certain circumstances.
Hackers use automated tools that make it easy to discover listening ports, and to identify the underlying application. It’s natural that these vulnerabilities are going to be more prevalent on the most commonly used applications, as well as applications that are likely to give them the most control. Which just happens to be most management ports (RDP, SSH), or ports that they can gain management access from (FTP, SMB). That’s why it’s important to remember, the only ports that should be open to the public are ports that are meant to serve the public.
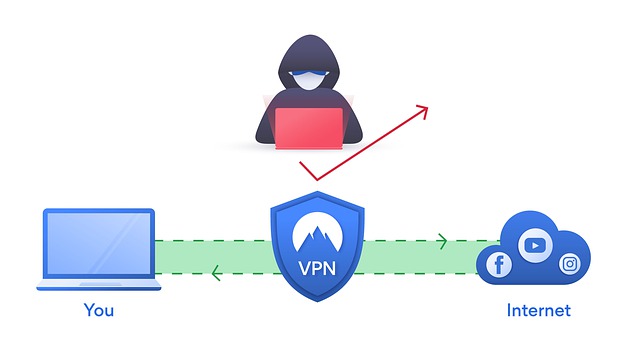
The only sure way to protect yourself is to offload access to these services via a dedicated VPN server. Whether that be a client VPN (SSLVPN) or Branch Office VPN (IPSEC). We could also deploy 2-Factor authentication for your SSLVPN service, which has the ability to authenticate with an Active Directory Domain. In rare situations, you may have a vendor that is not able to use VPN services. I don’t recommend locking down ports to specific source IP’s (because of spoofing attacks and human error), but if its your only option, it’s better than leaving ports open to the whole world.
Block4: Use a CDN Provider
While services like Cloudflare, Sucuri, Incapsula, etc., are known for their performance benefits, most of them also have security benefits, like DDOS protection, and Web Application Firewalls. But, the built-in security feature I want to focus on is the ability to hide the real IP of your server(s). Think of it like a P.O. BOX, whereas people sending you mail, don’t actually know where you live. When you use a CDN, all of your web traffic goes there first, and then that traffic gets proxied to your web-server. So effectively, clients only see the CDN and are oblivious to anything beyond that. The worst kind of hackers are looking for sites that process credit cards, and if they don’t know your servers IP, it reduces their attack surface, and they are limited to attacking your site through the CDN.
There are a few stipulations in making this effective.
- You can’t have any DNS records that point directly to your server(s) (they will be discovered). By default, your CDN usually proxies all requests, but you should check.
- You should enable the http-to-https redirection rule at your CDN. That way you only need to worry about 1 port open on your server, and that traffic is encrypted, so local packet sniffers aren’t a threat.
- You also need to lock down port 443 on your web server to your CDN providers IP ranges, because it is possible for attackers to scan the internet for your SSL by IP address. Your server will become virtually invisible to everyone, except your CDN.
Block5: WAF Services
By now, you should be feeling better about your security stance, and you would, if it was pre-2007. In the last decade, many attacks have been focusing on application vulnerabilities. Applications that were meant to be open to the public, but not meant to be vulnerable. Whether it be because of failed support for commercial software, developers that aren’t security focused, or hackers becoming more prevalent, it’s been clear that there is a problem. WAF services have since become a necessary measure to protect from SQL injections, Cross-Site scripting, and many other forms of attacks. If you can get a WAF service purpose built for your specific application, that’s even better. Another useful WAF feature to have is a Geo-location filter, which can be useful for blocking countries that are known to be malicious.
Block6: “Patch Tuesday”?
Most commercial software companies have a day where they release updates and security patches, and then publish that information to the public. So naturally, there are hacking websites devoted to this, reporting viable security flaws as they are released. Chances are, a good portion of these updates will never get installed, and these servers become victims. It’s unfortunate that pushing out updates/patches has the potential to break applications, and even more so that many consider it not worth the risk to install them.
But there is a way to install updates and patches with little to no risk. I highly recommend investing in a “Dev” server. It’s very easy for us to take a clone of your production server and redeploy it with new IP addresses. We also have a snapshot service, where we can take point in time snapshots before pending updates are installed, and then quickly roll them back should the update process fail at any point. To make things easier, Hostek can do the patching for you, just open a ticket and ask for more details.
Block7: Modern Antivirus

It’s not easy to protect your server from every possible scenario. The hackers goal is to place malware on your server by any means necessary. That’s why its important to have something locally installed to act as your last defense. A modern antivirus has the ability to protect from Malware in real-time as well as passively. However, you should know that Antivirus products can only block Malware that it already has samples of. It scans code against a library of code it knows to be harmful. That’s why it’s vital that you keep your Antivirus up to date at all times.
Block8: The Weakest Link
If you’ve ever had to pass a compliance scan, like PCI compliance, chances are you’re storing sensitive information. After you passed the scan, you probably even felt secure. It’s important to note that these scans only focus on the primary web server. Even though many eCommerce sites have at least 2 servers. Its the equivalent of installing a modern security system on the front door of your home, while leaving the back door and all of the windows unchecked. Every port and every application on every server are equally important, especially if they share a local network. Don’t let compliance become a false sense of security.
It’s unfortunate, but sometimes people can be the weak link. For example, using your web server as a client for searching the web, checking email, playing games, etc., is a bad idea. Don’t let friends or family borrow your servers to run their applications. Try to minimize who has access, and minimize the access they have. If an account does get compromised, we want them to cause the least amount of damage as possible. Your server should be purpose built, to do one job only.
Some more examples, don’t run web and SQL on the same server. Don’t use operating systems (Server 2008) that have reached end of life. Don’t create SMB shares over the public. Always use private VLAN’s for server to server communication. When possible, try to use services like GIT or Bitbucket to do change tracking, and to quickly deploy/redeploy your code. You want to leave the smallest footprint possible on your production servers.
Block9: Password Policies, Authentication, and Permissions
Enforcing password policies on servers should be the easiest to maintain, but it is often the easiest to overlook. Password brute-forcing is still very active, and it’s something I see often. As long as people aren’t following the rules, and computers become faster at guessing passwords, it will stay that way. Hopefully you don’t have publicly accessible applications that are susceptible to brute forcing, but you should prepare in case it happens by accident. Being proactive is the only way to protect yourself. I recommend searching for recommended password policies, but here’s some of my bare minimum favorites.
- Minimum of 13 characters with upper-case, lower-case, numbers, and symbols enforced. It will take a modern desktop up to 45,000 years, and a datacenter of super computers up to 5 years)
- If you have more than 2 Windows servers, implement Active Directory.
- Recycle server passwords every 180 days if local, 1 year if using Active Directory.
- Do not reuse the same password for multiple accounts
- Do not assign administrator level access to service accounts (FTP or web)
- Only apply bare minimum permissions for each account that needs access.
Block10: Annual Security Audits
Our Security audits are much different than what you would find on the internet. In fact, the initial process is to go through each of these building blocks, preparing each of your servers so they can pass our security audit. Because we have direct access to your servers, we are able to test more thoroughly. We also include the standard and extended penetration testing that other security firms offer. Our Advanced Security audit includes an examination from a Network Security Engineer, an Application Security Engineer (ColdFusion, WordPress, etc.), and a Database Engineer (SQL, MySQL)
The first thing we do is limit access to ports, shrinking the attack surface to its smallest point. Then we focus on the point that is susceptible, and we make it looks like its somewhere else (CDN). We give the option to add WAF services, and we secure the local server to the CDN. We do a follow up penetration test and make sure that every port is closed, unnecessary services aren’t running, and that TLS/SSL encryption is at its optimal level. We check OS updates, application patches, backups, antivirus, etc. We also investigate your logging and event viewer history, and make sure they keep adequate history. If you need any more information please don’t hesitate to open a ticket.
In Conclusion
There are a lot more security best practices I was not able to cover. One of the biggest is making sure your development team is constantly modernizing their code. I have yet to see a server get hacked that had operators being proactive about security. Every time I do a cleanup, or investigate an infection, there’s usually more than one reason why it happened.
I’m sure many small-to-medium sized businesses feel like a security specialist is out of reach. At Hostek, we have been putting together MSP programs that make this type of service available to you. At the very least you should make sure someone experienced looks at your services periodically. If you have any questions, or would like a consult, please call our sales managers at 18003079396.
Click here to order a hosting or domain name at an affordable price from our partners https://www.hoststar.at/ and https://www.hoststar.ch/!
Tags: Windows VPS HostingCategories: Business Tips, Developers, Hosting, Windows VPS Hosting


